Dns Server Spoofed Request Amplification Ddos
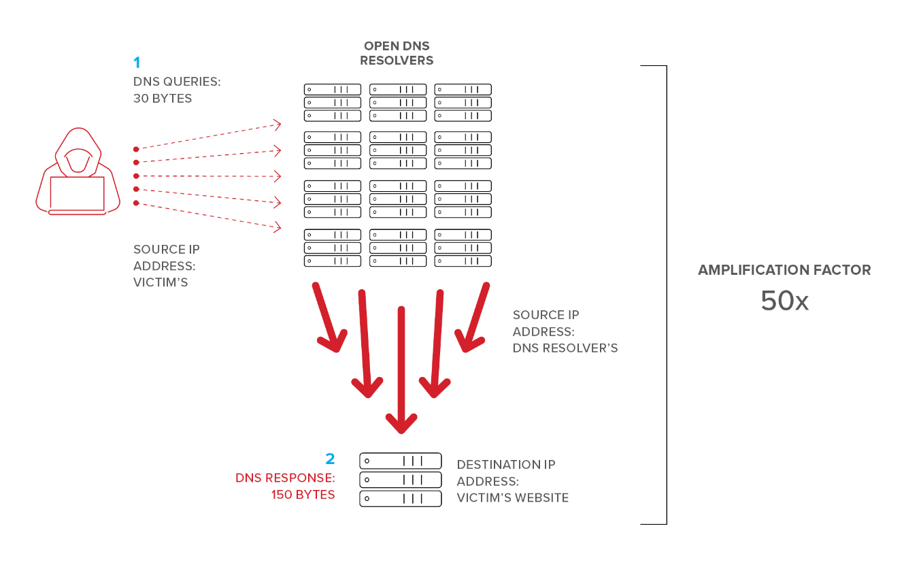
The DNS query was 17 bytes long the answer is 449 bytes long. A distributed denial-of-service DDoS attack is an attack in which the multiple compromised devices attack a target and cause the denial of service for users of the targeted device.
Dns Amplification Ddos Attack Cloudflare
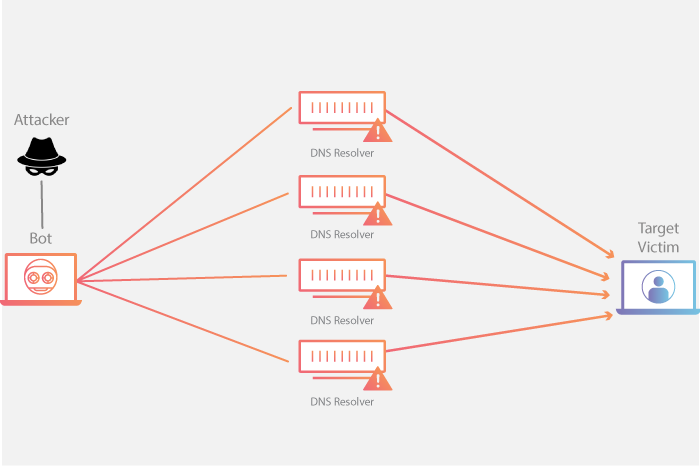
In a DNS amplification attack a large number of DNS request are sent with a spoofed from-IP-address to one or more DNS servers.

Dns server spoofed request amplification ddos. The goal is to flood the website with fake DNS lookup requests that consume network bandwidth to the point that the site fails. A DNS reflectionamplification distributed denial-of-service DDoS attack is a common two-step DDoS attack in which the attacker manipulates open DNS servers. The remote DNS server answers to any request.
The remote DNS server answers to any request. With enough spoofed requests coming from enough open DNS resolvers the recipients. DNS Server Spoofed Request Amplification DDoS.
DNS Server Spoofed Request Amplification DDoS Synopsis The remote DNS server could be used in a distributed denial of service attack. Nmap -sU -p 53 --scriptdns-recursion. The remote DNS server answers to any request.
DNS amplification DoS attack A Domain Name System DNS amplification attack exploits open DNS resolvers by performing a spoofed query of all record types for a given domain. DNS Server Spoofed Request Amplification DDoS Synopsis. So it is important to protect servers from DDoS to avoid server downtime.
This DDoS attack is a reflection-based volumetric distributed denial-of-service DDoS attack in which an attacker leverages the functionality of open DNS resolvers in order to overwhelm a target server or network with an amplified amount of traffic rendering the server and its surrounding infrastructure inaccessible. What is a DNS amplification attack. DNS amplification is a type of DNS attack that performs Distributed Denial of Service DDoS on a target server.
The susceptibility to this type of attack is generally due to consumers or businesses having routers or other devices with DNS servers misconfigured to accept queries from anywhere instead of DNS servers properly configured to provide. The remote DNS server answers to any request. DNS Server Spoofed Request Amplification DDoS.
A Domain Name Server DNS amplification attack is a popular form of distributed denial of service DDoS that. By spoofing the source IP address a remote attacker can leverage this amplification to launch a denial of service attack. One of my Windows Server 2008 R2 Standard Service Pack 1 is running with active directory and when scan the the server i got the below mentioned vulnerability.
DNS Server Spoofed Request Amplification DDoS Synopsis. The remote DNS server could be used in a distributed denial of service attack. The DNS query was 17 bytes long the answer is 449 bytes long.
During DDoS a targeted system is flooded with incoming messages connection requests or malformed packets in order to slow downcrash the system or to exhaust the network bandwidth. It is possible to query the name servers NS of the root zone and get an answer that is bigger than the original request. Please support me on Patreon.
It involves cybercriminals exploiting publicly available open DNS servers to overwhelm a target with DNS response traffic. DNS reflection involves abusing misconfigured DNS resolvers that respond to spoofed requests. To perform DDoS attacks via amplification attackers will use very small DNS requests to return answers that are many times larger amplified.
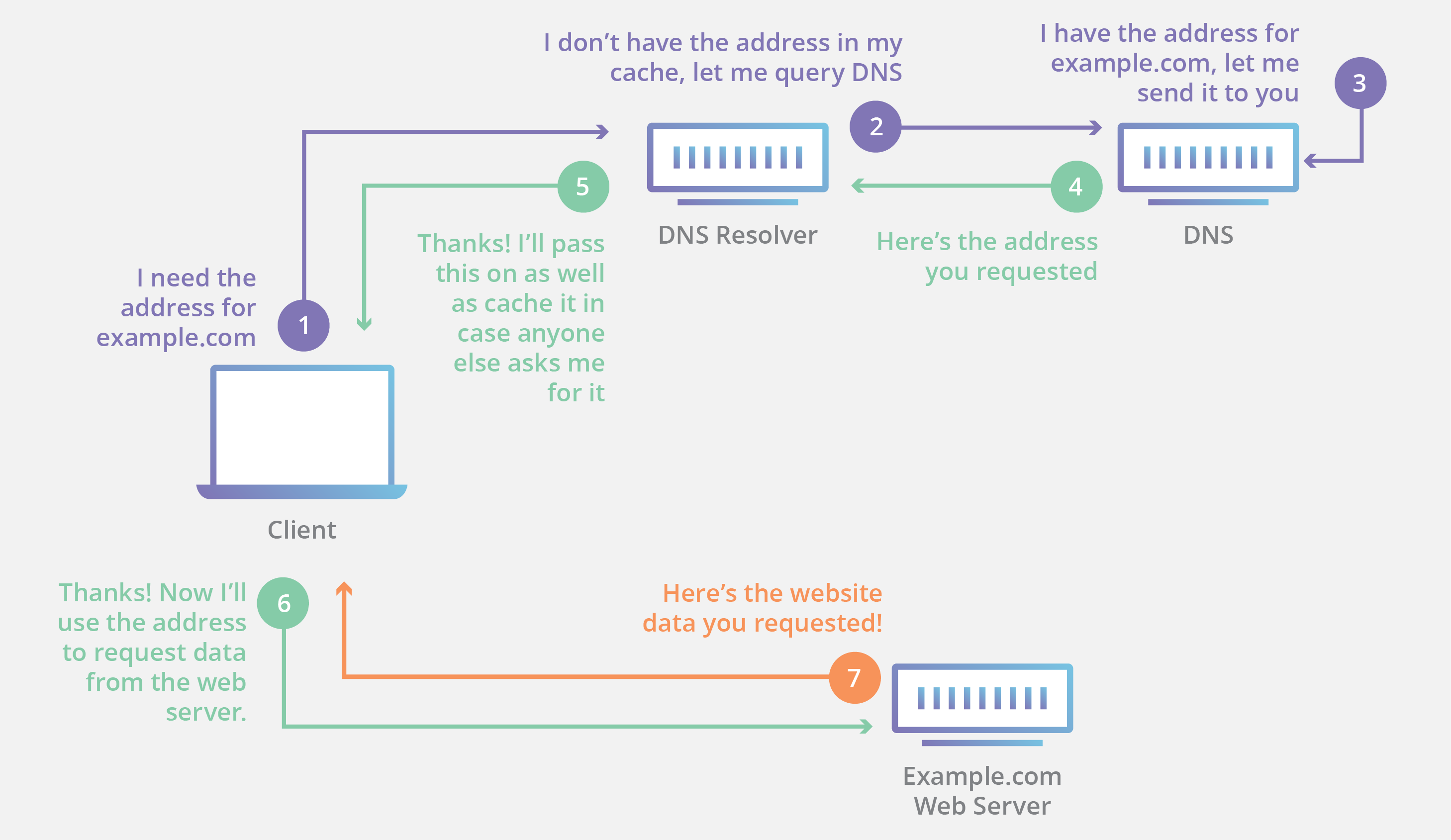
Depending on configuration these DNS servers will send a response back to the IP address that the request appeared to originate from. In a DNS amplification attack malicious actors take advantage of the normal operation of the Domain Name System DNSthe address book of the Internetusing it as a weapon against a targeted victims website. A Domain Name Server DNS Amplification attack is a popular form of Distributed Denial of Service DDoS in which attackers use publically accessible open DNS servers to flood a target system with DNS response traffic.
The effectiveness of this attack can be increased by employing a DDoS component as well by sending requests to multiple open resolvers simultaneously. DNS amplification is a Distributed Denial of Service DDoS attack in which the attacker exploits vulnerabilities in domain name system DNS servers to turn initially small queries into much larger payloads which are used to bring down the victims servers. DNS server spoofed request amplification DDOS.
DNS Server Spoofed Request Amplification DDoSHelpful. It says restrict access to your DNS server from public network or reconfigure it to reject such queries - how do i do this. In order to secure a DNS resolver against this type of attack it should be made to either not permit recursion or to only accept recursion.
It is possible to query the name servers NS of the root zone and get an answer that is bigger than the original request. The primary technique consists of an attacker sending a DNS name lookup request to an open DNS server with the source address. The cybercriminal first uses a spoofed IP address to send massive requests to DNS servers.
This DNS server then sends a DNS response packet back not to the hacker but to the spoofed IP address. The initial request is forged so that it appears to be coming from the victims IP address and in turn the DNS server sends the amplified response to the victim. Description The remote DNS server answers to any request.
Description The remote dns server answer to any request. By spoofing the source IP address a remote attacker can leverage this amplification to launch a denial of. By spoofing the source IP address a remote attacker can leverage this amplification to launch a denial of service attack.
The DNS server then replies to the request creating an attack on the target victim. It is possible to query the name servers NS of the root zone and get an answer which is bigger than the original request. Therefore an attacker that is able to spoof a victims IP address can have a DNS request bombard the victim with a 100-to-1 ratio of traffic coming back to them versus what was requested.
The remote DNS server could be used in a distributed denial of service attack. By spoofing the source IP address a remote attacker can leverage this amplification to launch a denial of service attack against a third-party host using the remote DNS server. This DNS response packet may be many times larger than the DNS query packet and this way the DNS server amplifies the traffic sent to the victim.
The attacker sends a DNS lookup request to an open DNS server where the source address is spoofed to become. It is possible to query the name servers NS of the root zone and get an answer which is bigger than the original request. Attackers can send DNS queries to these servers on.
It is expected that recursion will be enabled on your own internal nameservers. It is possible to query the name server of the root zone and get an answer that is bigger than original request. Checks if a DNS server allows queries for third-party names.

10 Simple Ways To Mitigate Dns Based Ddos Attacks

General Architecture Of A Dns Amplification Attack Download Scientific Diagram

6 Dns Amplification Attack A Real World Example Youtube

Sflow Dns Amplification Attacks
Do You Know If Your Dns Server Can Be Used For Ddos Attacks Black Hills Information Security

Udp Reflection Attacks Aws Best Practices For Ddos Resiliency

An Example Of A Dns Amplification Attack 4 Download Scientific Diagram

Anonymous Dns Amplification Attacks For Operation Global Blackout Security Affairssecurity Affairs

Figure 1 From Detection Of Ddos Dns Amplification Attack Using Classification Algorithm Semantic Scholar

Dns Amplification Attack 4 Download Scientific Diagram
Dns Reflection And Amplification Attacks Cyberhoot

Dns Amplification Ddos Attack Download Scientific Diagram

Ddos Video What Is The Future Of Ddos Attacks

Dns Reflection And Amplification Attacks Cyberhoot
Dns Server Spoofed Request Amplification Ddos

0 Response to "Dns Server Spoofed Request Amplification Ddos"
Post a Comment